In today’s interconnected world, organizations heavily rely on a vast array of network devices to keep their operations running smoothly. From computers and servers to printers, routers, and surveillance cameras, these devices form the backbone of modern business infrastructure. To effectively manage and maintain this complex system, it is crucial to have a clear understanding of all the devices connected to it. In this article, we will explore how to scan a network for devices using Total Network Inventory (TNI), a powerful tool that simplifies the process of discovering and organizing devices across your network.
Why do you need to scan the network for devices?
Before delving into the process of inspecting devices on a network, it is essential to first understand why this procedure is so important. Here are a few key reasons:
- Accurate asset management enables informed decision-making regarding hardware upgrades, maintenance schedules, and resource allocation. A clear understanding of the network architecture is also essential for planning expansions, optimizing performance, and troubleshooting issues.
- Regular device scanning helps identify unauthorized or rogue devices, reducing potential security risks. In today’s threat landscape, continuously monitoring the network for unknown devices is critical for detecting and addressing threats before they escalate.
- Finally, maintaining an up-to-date network map significantly speeds up troubleshooting. By providing IT teams with detailed information about connected devices and their configurations, issues can be identified and resolved more efficiently, minimizing downtime and ensuring smooth operations.
What methods can be used to scan a local network using TNI?
Total Network Inventory offers several methods to scan local network for devices, catering to various operating systems and device types:
- WMI scanning. A standard set of interfaces for accessing devices, applications, and parameters on Windows. This method leverages the Windows Management Instrumentation (WMI) framework to collect detailed information about Windows-based devices on the system. By using WMI scanning, TNI can gather data about hardware specifications, installed software, and configurations, providing a comprehensive overview of the Windows devices connected to the network.
- Remote scanning via SMB protocol. Collects comprehensive information about the scanned system by remotely running an agent with the necessary local privileges. This method involves deploying a lightweight agent to the target device, which then collects detailed data about the system and sends it back to the TNI server.
- Remote scanning via RPC protocol. This method uses the Remote Procedure Call (RPC) protocol to communicate with Windows-based devices and collect information about all of the installed applications and services. By leveraging RPC scanning, TNI can identify potential compatibility issues or outdated software versions that may pose a risk to the network.
- Remote scanning using SSH protocol. Suitable for Unix and macOS. This method allows TNI to securely connect to Unix-based and macOS devices using the Secure Shell (SSH) protocol. By establishing an encrypted connection, TNI can safely collect detailed information about the device’s hardware, software, and configuration settings without ever compromising the security of the network.
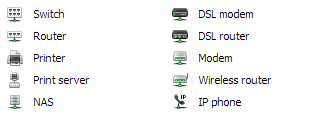
- Remote scanning using SNMP protocol. Ideal for printers, managed switches, routers, xDSL modems, IP phones, and wireless access points that support SNMP. The Simple Network Management Protocol (SNMP) is a widely supported standard for monitoring and managing system devices. By using SNMP scanning, TNI can gather detailed information about the status, performance, and configuration of these devices, enabling IT teams to proactively and efficiently monitor and maintain the network infrastructure.
- Low-level hardware scanning. For more comprehensive system analysis, TNI offers an advanced scanning method that accesses low-level hardware data directly through system APIs, retrieving details such as memory module information and hard disk specifications. This method provides even greater detail about the hardware components of each device on the network, enabling IT teams to make smart informed decisions about upgrades, replacements, and capacity planning.
- Manual addition. Allows administrators to add devices that cannot be automatically detected. In cases where a device does not support any of the automated scanning methods, IT professionals can manually add it to the inventory to ensure all assets are properly documented.
By offering such a wide range of scanning methods, TNI provides organizations with the flexibility to discover network devices in a way that best suits their specific requirements and infrastructure. Whether dealing with Windows, Unix, or macOS systems, or managing a variety of web devices, TNI has the tools that are necessary to create a comprehensive and up-to-date inventory of all connected assets.
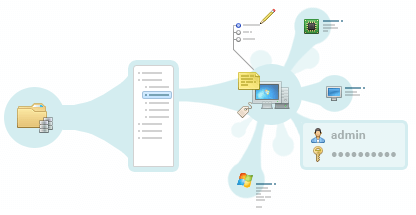
Scan the network with the IP address scanner
TNI’s IP address scanner is a versatile tool that works with both Windows and Unix operating systems as well as non-standard net equipment using various protocols. Once the scan is complete, TNI provides detailed information about each device, including its hostname, operating system, and network configuration.
It is worth clarifying that the software allows you to work with various equipment: network-attached storage devices (NAS), printers, routers, switches, UPS devices, VOIP phones, and web servers based on various operating systems. The scanning algorithm is almost the same for all devices (it only differs in the equipment protocol).
Scanning Windows-based devices
There are three scanning methods available for Windows devices:
1. Remote scanning via SMB protocol:
- Downloads the tniwinagent.exe file to the admin shared folder on the remote PC.
- Connects to the Service Manager of the remote computer, installs, and starts the agent as a service.
- The agent scans the system, saves the collected information to a compressed file, and then stops.
- The main module imports the resulting file into its storage.
- The agent service is uninstalled and then the executable file is deleted.
2. Remote scanning via RPC protocol:
- TNI’s main module connects directly to the target computer’s WMI service.
- Information is collected remotely via the RPC protocol.
- This method may generate significant network traffic and can result in slower scanning speeds on networks with limited bandwidth.
3. Resident agent scanning:
- The resident agent is installed permanently on the target computer.
- The agent runs as a Windows service and performs scans according to a configured schedule or on demand.
- Collected system information is stored locally and transmitted to the TNI main module when the connection is available.
- This method reduces network traffic during scanning and is especially suitable for remote or mobile devices that are not always connected to the local network.
- The resident agent ensures regular and automated inventory updates without requiring repeated remote deployment.
Scan different operating systems
Linux, Unix, and macOS
Checking computers running macOS, Linux, FreeBSD, and ESX/ESXi is carried out using an executable file downloaded to a remote PC via SSH and SCP/SFTP. Before starting a scan, ensure that:
- The remote computer is running an SSH-2 server with SFTP or SCP support, and the firewall allows access to it.
- The user performing the scan is allowed access to the SSH server.
- The user has administrator rights (for Linux OS, if not root, must be in the sudoers list).
The scanning process:
- TNI connects to the remote computer using the specified protocol and transfers the scan agent to a temporary folder in the user’s home folder.
- The agent starts, collects information about the network, and then creates a file with the gathered data.
- The file is transferred back to TNI and imported into the inventory database.
- The temporary folder with the agent and the created file is deleted.
How to scan devices on a network using SNMP
SNMP Network Discovery Software collects detailed information about every router, switch, network printer and other equipment in a single pass. To start an SNMP scan, follow the same steps as with other scanning methods, but select the “SNMP” function in TNI.
Elevate network device scanning with Total Network Inventory
Total Network Inventory is a powerful tool that simplifies the process of scanning devices on the network. With multiple scanning methods and a user-friendly interface, TNI makes it easy to discover devices and maintain an up-to-date inventory of all assets.
By leveraging TNI’s capabilities, you can scan computer hardware and gain valuable insights into your network infrastructure. Whether you need to scan devices for security, asset management, or troubleshooting purposes, TNI provides the right tools to get the job done efficiently.
In conclusion, regularly scanning net devices is an essential practice for any organization that relies on a complex system infrastructure. By understanding what a network scan is and how to scan for devices across your network, you can ensure that your environment remains secure, well-managed, and optimized for performance. With Total Network Inventory, you can streamline your scanning processes and take control of your network like never before!