In today’s digital age, organizations heavily rely on their computer networks to carry out their day-to-day operations. As these networks grow in size and complexity, it becomes increasingly important to keep track of all the devices connected to them. This is where Active Directory domain auditing comes into play.
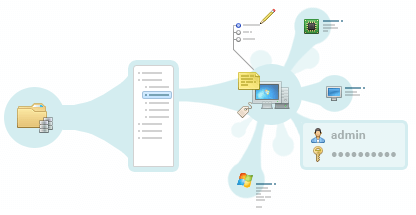
With TNI, administrators can quickly and easily create an inventory of computers in Active Directory and gain valuable insights into the state of their network. The software’s reporting capabilities make it easy to generate detailed reports on the hardware and software inventory, security status, and more.
These reports can be used to identify any potential issues and optimize the network for better performance. For example, by analyzing audit data, administrators can identify computers with outdated software or security vulnerabilities and take corrective action before they become a problem.
Furthermore, the network mapping feature in Total Network Inventory provides a visual representation of the network, making it easier to understand its structure and identify potential bottlenecks or areas for improvement.
While AD auditing can be performed manually, it is a time-consuming and error-prone process. Fortunately, there are software solutions available that can automate the process of Active Directory computer inventory and make it much more efficient. One such solution is Total Network Inventory.
Total Network Inventory is designed for organizations of all sizes that need to keep track of their Active Directory assets and personnel. Whether you have a small office with a dozen computers or a large enterprise with thousands of devices and employees, TNI can help you simplify the process of inventorying Active Directory computers while streamlining user account management.
Total Network Inventory is a comprehensive solution for inventorying computers in Active Directory environments. It can perform the following tasks:
In order to start scanning the network, you need to specify an OU (Organizational Unit) from your Active Directory domain and then click the start button. After a short period of time, you will receive a list of all the computers that meet the specified criteria. The scan time depends on the number of devices connected to the network, but usually, it takes no more than a few minutes. An intuitive interface shows the scanning progress.
Total Network Inventory provides detailed information about each device on the network, including:
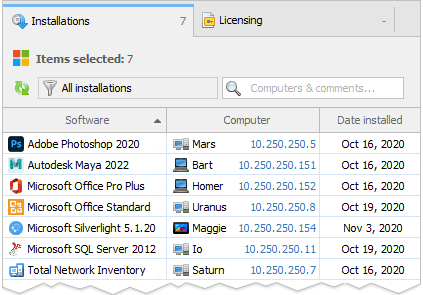
Total Network Inventory integrates closely with Active Directory to index organizational unit structures, import user attributes, track group memberships, and enable user-to-device mappings across the network. Customizable auditing reports provide visibility into AD user account status, inactive or disabled users, password expiration, group policies, and permission changes. Automated synchronization tasks further enhance auditing capabilities through change tracking and alerting on modifications.
Total Network Inventory can store employee information, such as name, address, photo, description, and other relevant details. This data can be automatically extracted from AD, simplifying the process of synchronizing user accounts with Active Directory.
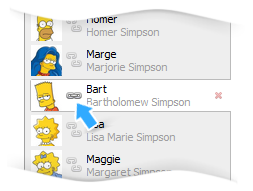
TNI has a special tab called "Users", where you can work with and manage user account data.
All network users are divided into three categories:
Only one user of any type can be assigned to each computer found on the network: a local user of this device, a domain user, or a manually created user.
Any field that contains user data can be added as a column to a table report. Viewing, managing, editing, and adding user information is just as easy as using other features of Total Network Inventory.
Before starting the scanning process, you can configure synchronization between Total Network Inventory and Active Directory. This can be done by going to the settings menu and specifying the domain controller. There you can also configure other audit settings, such as what to synchronize (computers or users) and what actions to take on computers that were discovered on the network but not found in AD.
If your environment requires encrypted directory access, you can enable the Secure connection option in the properties of any group that you want to synchronize with AD. When enabled, TNI connects to the domain controller using LDAPS (LDAP over TLS), ensuring that all communication between the program and the Active Directory server is encrypted.
Once you have added scan tasks and specified the nodes to scan, you can begin the synchronization process. For Active Directory, the nodes can be specified using the IP address or the name of the domain controller with the "AD:" prefix (e.g., "AD:10.0.0.1" or "AD: server name"). The generated report will contain information from the "Location" and "Description" columns if the domain administrator has filled out these details.
Once the scanning process is complete, some devices may appear in the program as stubs. These are created for computers that were found in Active Directory but were not scanned. Only basic information will be displayed for such computers, including the description, location, and OS version. These stubs can be rescanned later to obtain complete information.
If you are looking for a comprehensive solution for Active Directory inventory of computers and user management, Total Network Inventory 6 Professional is the perfect choice. With its advanced features and intuitive interface, TNI makes it easy to keep track of all the devices on your network and ensure that your IT infrastructure is secure, compliant, and optimized for performance.
Whether you are a small business owner, an IT administrator, or a Managed Service Provider, Total Network Inventory 6 Professional has the tools you need to streamline your Active Directory computer inventory and user management processes, allowing you to take full control of your network!